What You Can Learn From An All-Around Data Recovery Training Courses?
 Data Recovery Training course is to train you on advanced data recovery techniques as well as advanced data analysis strategies.
Data Recovery Training course is to train you on advanced data recovery techniques as well as advanced data analysis strategies.
You will do during the data recovery training class:
1. Logical Recovery of disabled hard drives
2. Using file format recognition tools
3. Logical recovery via avoiding BIOS interrupts
4. Motions that unlock the actuator of a drive
5. Diagnosing the physical recovery of drives
6. Comparing pre-recorded sound samples to live drives
7. Logic board replacements
8. Single and Multi-Platter Swaps
9. Head Assembly replacement
10. P-List and G-List recovery
11. Addressing SMART values
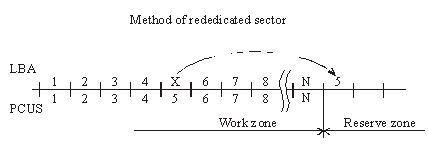
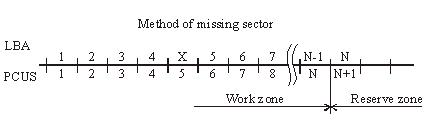
12. Dealing with damaged sectors
13. Reverse scanning
14. Capturing SID protected folders
15. Resolving kernel or driver issues with a Linux bootable disk
16. Head Stack replacement
17. Working with the Service Area (SA) of a drive
18. Reviewing data structures with a Hex Editor
19. Diagnosing “clicking noises”
20. Mac OS X Data Recovery
21. Linux Data Recovery
22. RAID 0 Recovery & RAID 5 Recovery
23. Vista and Recovery of Shadow Copies
24. Clearing passwords on a password protected drive
25. Solid state drive recovery
26. Firmware issues