SQL & SQL Database File Recovery
Microsoft® SQL server is a business enterprise software package that manages data through a client/server relational database. There are four fundamental aspects to a SQL (Structured Query Language) server.
1. Database File
2. Relational Database Concept
3. Client/Server System
4. Database Management System (DBMS)
The Database File refers to the physical file that contains the data the SQL server manages. This file is more than just a container for data. SQL files, or .MDF files, are highly organized and complex. The file is designed like this so that SQL server can handle multiple data transactions at once.
The Relational Database Concept is the method employed to organize the data; this is separate from the internal organization of the file itself. Relational Database Concept systems use mathematical set theory to organize the data in the most effective way. Data organization is critical to maintaining the speed of the database server.
The Client/Server System refers to the part of SQL server that communicates with the operating system. This part of the system needs to manage the server’s resources, connections and managing multiple databases at the same time.
The Database Management System interacts and works will all the above items. Not only does this manage the internal structure of the .MDF file, DBMS also controls the Relational Database side of things and organizes the data. The DBMS of SQL server is the heart of the system.
Data loss situations-What can happen?
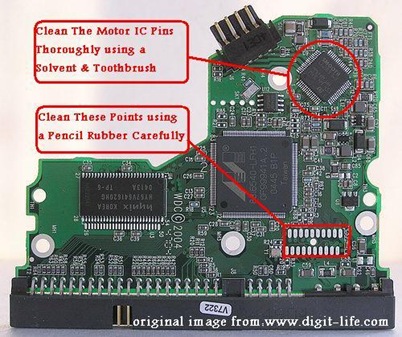
Data loss situations can occur at a number of different levels. The first level of data loss starts with the storage device. This can be a single hard disk or a SAN or RAID storage array. The second level of data loss can start at a file system level. The file system is a unique method of storing and organizing system and user files. The operating system controls the file system. If the information about where data files are on the volume are damaged or lost, then adjustments or repairs need to be completed at a file system level. Once the file system is repaired then the file’s data stream can be accessed correctly. Most operating systems have a utility that will automatically fix the file system. These utilities work to make the volume accessible. However, this can permanently damage the data stream of the file. The third level of data loss can occur within the file itself. As previously mentioned, .MDF files are quite complex. The internal structure can be corrupted to the point where the DBMS will not make the database available.
The solution to data disasters
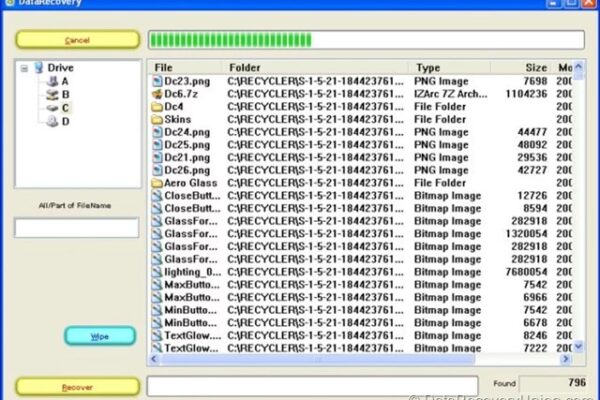
The process of a SQL recovery begins with finding the database file requested. If the database file is inaccessible due to problems with the storage device, then should work to get that data extracted. If the file is missing, deleted or truncated due to problems with the file system, then should work to adjust or repair the file system to correctly point to the data stream of the file. And finally if the file system has no pointers at all to the file, then should search the entire drive looking for SQL data.
The next stage is to work on the database file itself. This is where the SQL toolset comes. These tools analyze the complex internal structures of the .MDF file and provide reports as to what tables are recoverable. The reports also list the number of data rows that will come back.
Once the evaluation is complete and authorization is given to recover the data, the SQL toolset will copy the data into another SQL server database. After this phase is complete, we can backup or archive the recovered data.
Remote Data Recovery is the fastest solution for SQL recoveries. The Remote Data Recovery process will copy the recovered data into a SQL server that is setup on you or your client’s site. They only need SQL server running. For best results I recommend that the storage device we are working on be connected to a SQL server, because all of the data transactions will be occurring on a single machine.